APIPA
A PC gets an Automatic Private IP Addressing (APIPA) address when it cannot obtain an IP address from a Dynamic Host Configuration Protocol (DHCP) server. This typically happens due to one of the following reasons:
DHCP
Server Unavailability: If the DHCP server is down or unreachable.
Network
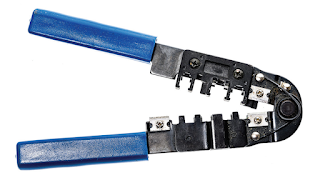
Issues: Problems with network connectivity, such as faulty cables or switches,
can prevent the PC from contacting the DHCP server.
DHCP Server Exhaustion: If the DHCP server has run out of available IP addresses to assign, the PC will not receive one.
New
router: One that isn’t RFC1542 compliant or a new router that doesn’t have
DHCP relay (IP Helper) enabled.
When
a PC cannot get an IP address from the DHCP server, it assigns itself an IP
address from the APIPA range (169.254.0.1 to 169.254.255.255). This allows the
PC to communicate with other devices on the same local network that may have an APIPA address, but it won’t be able to access the internet or other networks.